How to remove Cryptolock
Posted on Nov 20, 2013 by
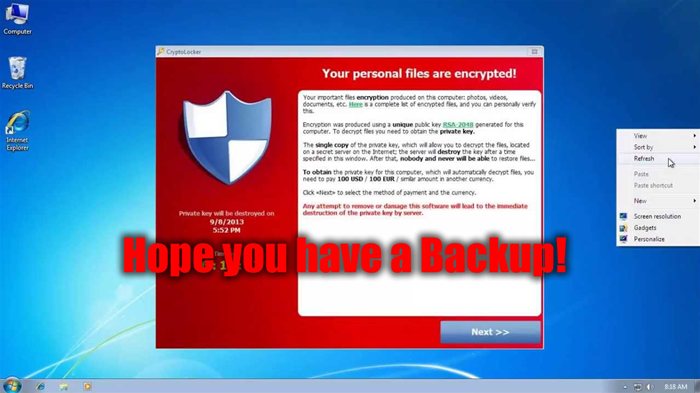
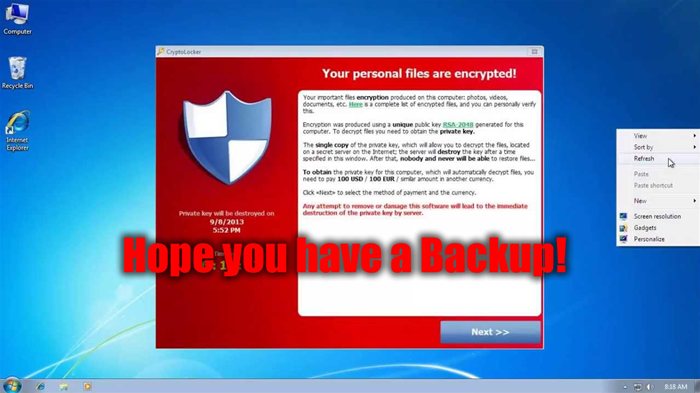
Paul WhiteA new wave of Ransomware has been infecting people's computers. Its called Cryptolock. I can show you how to remove it, but not how to restore your files. For that you need a backup. Windows Backup works well. If you have no backup you either pay the ransom, or accept the fact your personal data is gone, and start from scratch.
Just like a real virus in people. Cryptolock infects, does damage, and once you remove it, there is still damage left behind.
How it works
Once infected it will alert users with a red popup screen that tells them to pay $300 for the key to unencrypt their files. This payment is made via
Bitcoin or other non tracable monetary forms. The virus encrypts personal files with certain extensions ( JPG, PDF, DOC, and many more ). Pretty much any file you created is encrypted. However it doesn't seem to touch your programs, so you can still run most of your programs, although the files you created with these programs are now corrupt.
The bad news
Unfortunately unless you have a backup of your data, there is no way to just repair your corrupt files. They have been encrypted using a key. The only way to repair the files is to pay the ransom. However if you do have a backup of your data and just want to remove the virus continue with this guide. I successfully used this process to disable the virus, and remove it from my system. Then using a backup we restored our personal files to their state 24 hours ago.
Removing it
You can't just goto taskmgr and kill process. It pops right back up. Two processes are running, which restart each other when one is shutdown.
How to remove the virus
you can't delete the file, but you can change the extension. So find the file on your computer
usually located at C:usersyour user nameAppDataLocal
The file will have a weird name ( not even really a word ). change the extension of the file from .exe to .exe2
If you don't see the extension you need to goto
tools > folder options > View Tab and uncheck "hide extensions for known file types", then click apply and OK
Now you can go back to taskmgr and kill the 2 running processes.
Then you can delete the original file.
This surprized me, that I couldn't delete the file while running, but I could change the file extension.
The red box on all your screens is just a background image.
Right click on your desktop > Personalize, and selected a different background.
Then you can delete the image file from your desktop.
I also recommend using a program like CCleaner, to remove its startup instances from your computer.
Then reboot, and you are done.
Repairing after an infection
unfortunately every file that it has encrypted is no longer usable. This is where having a backup of your data comes in handy. I was able to use Windows backup to restore all my files to their originals from a day ago. Yes anything you have worked on since your last backup is gone, but its better than taking an entire day to reinstall your entire operating system from scratch. If you don't have a backup, then either you pay their ransom, or you accept the fact
Conclusion
People demand freedom without government ( NSA ) knowing what is going on. Whenever there is a way to abuse freedoms, Criminals will take advantage. I see Ransonware like this as the beginning of the end of
Bitcoin. All it takes is for a few criminals to abuse a system, for the government to step in and validate shutting it down. Especially when said randomware infects government computers.
Bitcoin's value has skyrocketed in the past month, I suspect much of this demand for
bitcoin is based on paying the ransom.
Discussion
No Comments have been submitted
 WhiteSites Blog
WhiteSites Blog